People are always asking me to tell “hacking” stories, since there are so many of them…I’m going to focus specifically on password related stories. Here is a top 3 countdown to the craziest password story I have.
#3 – Bad passwords
Yeah, yeah, yeah, I know everyone has heard this a million times, but let’s discuss it from a hacker’s perspective. I’ll start by saying most password policies suck and here is why.
Let’s examine a typical password policy.
8+ Characters
3 or more of the following
- Upper Case Letters
- Lower Case Letters
- Numbers
- Special Characters
Password must be changed every 90 days
These types of password policies actually encourage easy to guess passwords that tend to be use by multiple users. This gives me the ability to easily extrapolate your most common passwords based on what I know, and use this to break into your corporate network. Here is how it works:
Employees like to use predictable passwords and bad guys use this to perform password guessing attacks against a large group of users. This is an extremely common vector that still works against almost all companies. The basics are this, we enumerate users (generally through linkedin and google)…then find a login portal most users are all likely to have access to and guess 1 password against all of the users. Traditional brute force techniques one one-user-at-a-time, cause the user to get locked out and trip alarms. Good hackers avoid alarms. A reverse brute force or password spraying attack tends to evade detection and provide almost guaranteed access to most networks.
One time we identified a few passwords we felt most likely to get us access to this network. (In this case we were performing the attack against Outlook Web App) – This particular time we guessed 1 password (it was something like Summer16) and used it against 800 user accounts. We logged onto about 50 user accounts with this exact same password. Of those users, we identified 15 with VPN access, and 2 with local admin access. We were able to use the VPN access to compromise the 2 machines with local admin access, dump the local admin credentials. This company was reusing local admin passwords across multiple systems. This gave us the ability to spread to key user systems to gain domain admin rights–control over the domain controller. Game Over – The entire attack from start to domain admin took less than 3 hours.
The moral of this story is that weak or guessable passwords are a major cause of data breaches and tend to be an easy way into any network that doesn’t enforce multi-factor authentication. Password length is significantly more important than complexity. My advice is to forget about password complexity and just make all of your passwords longer. Use a phrase and keep it over 15 characters.
Don’t let the possibility of dictionary attacks [link to definition] overshadow their real world frequency. Those that neglect the human factor get burned by their own tech. Passphrases yield greater assurance without the unintended human consequences.
One other moral – Never reuse local admin passwords – this a guaranteed way to turn an isolated incident into a domain breach. Check out the Microsoft LAPS tool if you need help managing unique local admin passwords.
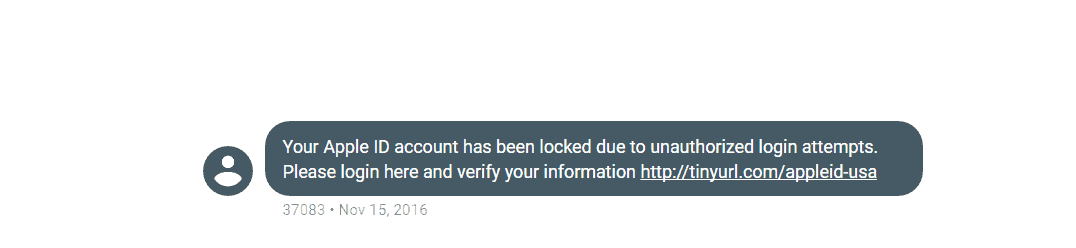
#2 – Phishing 4 Passwords
Phishing is a guaranteed way to get users to give up passwords, one-time passcodes, infect their computers or hand over countless other forms of sensitive information. This is every hacker’s go-to move to gain access into your organization’s networks. Not only do they gain access to your network, but they gain the level of access the user’s they phished have. This single attack can bypass most of the organization’s security controls designed to keep hackers out.
So, here is how I get your users to give me their credentials and a backdoor into their employer’s network in a single attack.
First, I craft an email telling your users about some technology upgrade that was performed the previous night and tell them that they can access it and check out the new tech if they choose. I’ll then provide them with a web page that looks very real like login.microsoftweblogin.com (I actually own microsoftweblogin.com). At this website I’ll clone a legitimate login page and put a keylogger on the page. Now when the user types their username and password I’ll see what they type as they type it. Next I add a nice application addon that prompts the user to open run it. This application might be called something like “Microsoft Web Essentials”. So the browser asks them something to the regard of: “Would you like to run Microsoft Web Essentials?” When the user clicks run I have a backdoor on their system. From this point it’s only a matter of time until we get complete control of your networks and systems.
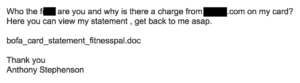
#1 – How to get domain admin over the phone
This story is hilarious, but a cautionary tale nonetheless. During our assessments we test human weaknesses as well as computer weaknesses. As part of this testing we make phone calls to get information, (such as password policy) or to get users to go to our site and run our custom malware that gives us backdoor access to their machine. On one such occasion I called up hoping to get a help desk technician to go to my site that hosts my malware. This is where it gets interesting.
This is a law firm – So obviously I call in pretending to be a Partner in the firm. I tell them about how I’m trying to run this analytics software a stock market analyst buddy of mine shared with me and how it won’t run. (We had already discovered that application whitelisting security software was preventing unknown, unapproved software from running on their endpoints.) At this point the helpdesk employee interrupts my plea for help and says “It’s okay, just use my account” –He proceeds to give me his username and password over the phone.
Facepalm! – His password was Password1
Next, I take those credentials and I log into the VPN that we discovered during our recon where we learn everything we can about the company and what it has on the internet. Voila – the credentials work. Now I am on the network and we use the credentials to compromise the machine of the helpdesk employee we were talking to and immediately discover that these credentials were in the “Domain Admins” group and that we just compromised the entire domain “Over the phone!”
This is an extreme example with the obvious lessons: don’t give passwords over the phone; don’t even share them with your everyday peers.
But the less obvious lesson, hackers don’t just exploit human trust. We also exploit fear. I’m confident this person had been bullied many times by VIP’s in that law firm. So, this is yet another example where tech burns those failing to account for human weaknesses. Worse, this non-technical root cause is just the sort of thing executives excel at fixing. The C-suite must ensure that all employees, especially themselves and other VIP’s, know that the C-suite has the backs of all those that enforce cyber policies.
This example also illustrates another lesson. The help desk person violated policy. Policies atrophy to uselessness if they are not exercised, measured, and reported. The law firm assumed its policies were consistently enforced. Our pen test proved otherwise. Our client learned something useful before something catastrophic happened. BTW, if your organization relies only on traditional pen tests to test your organization’s human readiness, then it’s not cyber ready. I’ve love to see a good survey on this. I’d be shocked if more than 10% of enterprises exercise, measure, and report the human readiness underlying more than a few of their cyber policies.